Turning Off Buzz is far more difficult than you may think infact it's a nightmare. First it's really hard to find the Turn Off buzz link which is located at the last place the user will look for which is at the very bottom of the page.
Update: Google has now given an option to Disable the Buzz in "Edit Profile" section.
Now that you have found out the link to disable Buzz don't hurry in doing so, as this will mean that your jabbering will still be publicly available and people will still be following you.Go to the Buzz section in your Gmail and delete all the comments and postings you have made.
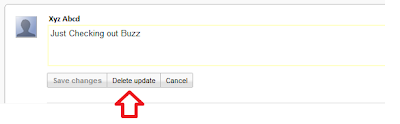
Update: The "Delete profile and disable Google Buzz completely" option in Edit Profile has been added and will also delete all your post now though I am not sure about the comments.
Remember even after doing so your comments and posts will still be available in the inbox of persons who were following you. And there is nothing you can do about this. Now here's when you realize that the saying that "Quarrels end, but words once spoken never die" is so true (don't know who said it).
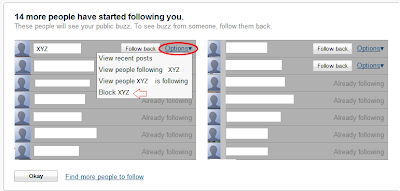
Now go to the Buzz section it will show you all the persons that are following you and vice versa. Now you will have to go to each and individual user click on options and select Block User , this will not send them any notification or message but will silently block them from your postings. If you have a huge fan following you have one of a hell task ahead to block them all as there is no simple option to block them all.
Update: Until this morning there was no option in Buzz to block those followers who didn't had any public profile. But now Google had introduced that option finally, hope Google addresses other concerns also quickly.
After you are done with all this you can go and disable Google Buzz by clicking on Turn Off Buzz from the bottom of the page.
 Update: Google has now given an option to Disable the Buzz in "Edit Profile" section.
Update: Google has now given an option to Disable the Buzz in "Edit Profile" section.
Lets hope that Google will introduce the basic privacy features in Buzz and then I think some of the people who have turned off Google Buzz may turn it on once again though I am not very sure of the later. Share with me what do you think about Google Buzz and do you think it can take place of twitter.
Update: Google has made many settings appear more prominently and has introduced some privacy feature, still long way to go Google.